Cybersecurity & Recovery
With intentional threats on the rise, prepare for the worst and rest easy knowing we have your back with cybersecurity and recovery.

Compliance Does Not Guarantee Security
Security is all about risk management. Understanding the intricate relationships between rules, regulations, standards, and policies is a complex undertaking. To have the best security solutions in place, you need to be compliant with legal and industry regulations, and you need to ensure your internal framework and processes align across the organization for governance, risk, and compliance controls. Breaches are often caused by small, overlooked gaps in processes, and those with ill intent know exactly how to exploit them.

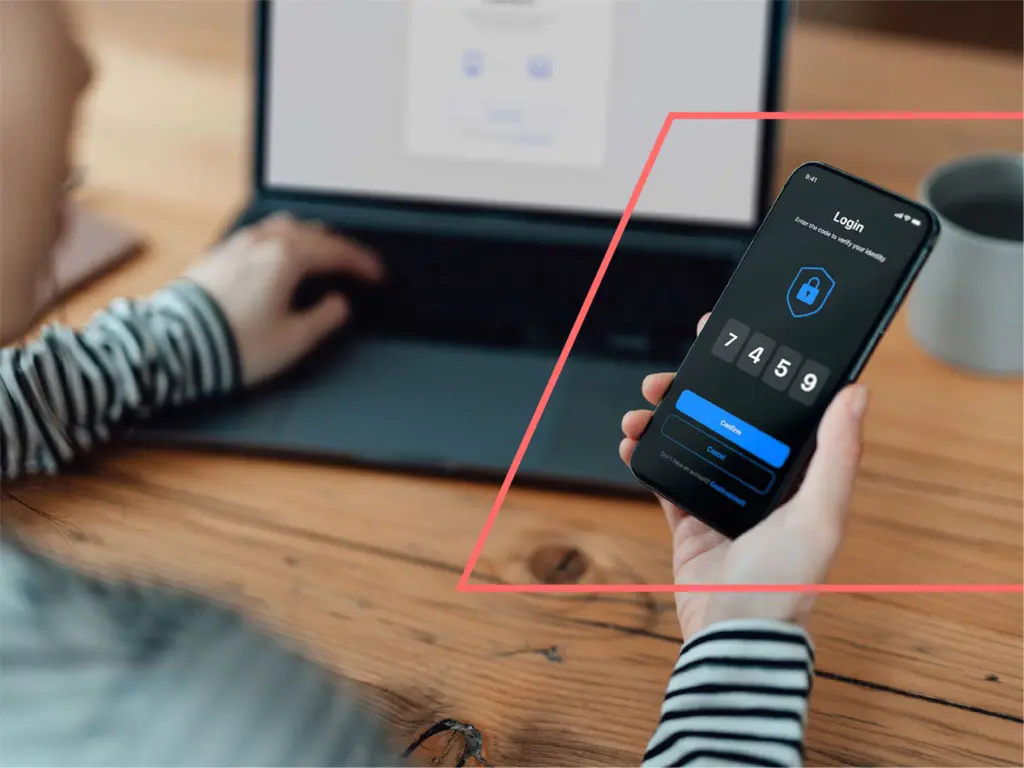
A People-First Approach to Cybersecurity
IT professionals are no longer just protecting data against unintentional corruption and disaster. With over 2,220 cyberattacks each day in the U.S. alone, we know cybersecurity is not perfect, and there are constant methods to find holes in security measures. Our approach to cybersecurity considers the laws, regulations, and guidelines and also investigates the way your organization accesses and uses the data you need to protect. Considering the human process helps to find the gaps that can be exploited and leave you vulnerable. We create solutions to ensure your resources are being accessed by the right people at the right times.
Cyber recovery adds an additional layer of protection compared to disaster recovery. By pushing data to an isolated system (a “cyber vault”) with immutable storage and advanced analytics to isolate anomalous data, your organization can save a comprehensive copy of clean data that can be used to restore your production environment in the case of ransomware or other cyberattacks. While a cyber recovery solution may have a longer recovery point objective (RPO) and recovery time objective (RTO), it can ensure that you don’t have to pay a ransom for your data and that you can effectively recover from other devastating disasters.

Are you at risk for a cyberattack?
A cyberattack occurs every 39 seconds. The reality is that cyberattacks occur so frequently that it is not a matter of if but when it will occur.
Multiple Ways to Build a Solution
Just as every enterprise is unique, so must your security solutions. At Vervint, we offer multiple ways to assess your risks and build a solution that fits your exact needs.
-
Identity & Access Management Consulting
IAM ensures the right individuals have access to the appropriate resources at the right times for the right reasons. IAM consultants provide expertise in designing, implementing, and optimizing identity solutions tailored to an organization’s unique needs.
-
Backup as a Service
Our BaaS solutions are designed with simplicity, scalability, and security in mind. We ensure that the infrastructure supports automated backups, easy data retrieval, and seamless integration with clients’ existing systems. With an eye on cost efficiency, security, and 24/7 support, our team protects your data and makes it simple to recover.
-
Penetration Testing Services
Our penetration testing services act as a simulated cyberattack against your system from an external perspective to check for exploitable vulnerabilities. Vervint seasoned professionals use the latest tools and techniques to simulate real-world attack scenarios.
-
Vulnerability Assessments
Get a comprehensive overview of your system’s vulnerabilities, from software bugs to misconfigurations. We can help you understand vulnerabilities are critical and need immediate attention. Overtime, continuous monitoring and regular assessments ensure that you’re always one step ahead of potential threats.
Stay Ahead of the Threat with a Comprehensive Security Mindset
Build a People-First Cybersecurity Solution for Ultimate Protection
From regulations and compliance to people and processes, we are here to build a cybersecurity solution that keeps you safe and builds a cost-effective backup system.